Hacking always involves tools. A good hacker knows how to use tools to
his best advantage. An even better hacker writes his own tools. Here I
have listed the top 10 most popular tools used in hacking. It is
advisable to master these tools to become a good hacker. Note that all
the tools listed here are completely free.
1. Nmap
Nmap is also known as the swiss army knife of hacking. It is the best port scanner with a lot of functions
In hacking, Nmap is usually used in the footprinting phase to scan the
ports of the remote computer to find out wich ports are open.
2. Wireshark
Wireshark is a packet sniffer. It captures all network traffic going
through a network adapter. When performing man in the middle attacks
using tools like Cain, we can use Wireshark to capture the traffic and
analyze it for juicy info like usernames and passwords. It is used by
network administrators to perform network troubleshooting.
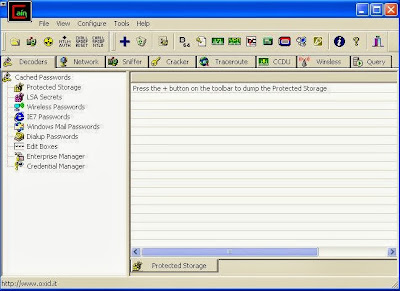
3. Cain and Abel
Cain and Abel is a multipurpose windows only hacking tool. It is a bit
old now, but it still does the job well. Cain can be used to crack
windows password, perform man in the middle attacks, capture network
passwords etc.
4. Metasploit
Metasploit is a huge database of exploits. There are thousands of
exploit codes, payloads that can be used to attack web servers or any
computer for that matter. This is the ultimate hacking tool that will
allow you to actually "hack" a computer. You will be able to get root
access to the remote computer and plant backdoors or do any other stuff.
It is best to use metasploit under linux.
5. Burp Suite
Burpsuite is a web proxy tool that can be used to test web application
security. It can brute force any login form in a browser. You can edit
or modify GET and POST data before sending it to the server. It can also
be used to automatically detect SQL injection vulnerabilities. It is a
good tool to use both under Windows and Linux environments.
6. Aircrack-ng
Aircrack-ng is a set of tools that are used to crack wifi passwords.
Using a combination of the tools in aircrack, you can easily crack WEP
passwords. WPA passwords can be cracked using dictionary or brute force.
Although aircrack-ng is available for Windows, it is best to use it
under Linux environment. There are many issues if you use it under
Windows environment.
8. Nessus
Nessus is a comprehensive automatic vulnerability scanner. You have to
give it an IP address as input and it will scan that IP address to find
out the vulnerabilities in that system. Once you know the
vulnerabllities, you can use metasploit to exploit the vulnerablity.
Nessus works both in Windows and Linux.
10. THC Hydra
Hydra is a fast password cracker tool. It cracks passwords of remote
systems through the network. It can crack passwords of many protocols
including ftp,http, smtp etc. You have the option to supply a dictionary
file which contains possible passwords. It is best to use hydra under
linux environment.
9. Netcat
Netcat is a great networking utility which reads and writes data across
network connections, using the TCP/IP protocol. It is also known as the
swiss army knife for TCP/IP. This is because netcat is extremely
versatile and can perform almost anything related to TCP/IP. In a
hacking scenario, it can be used as a backdoor to access hacked
computers remotely. The use of netcat is limited only by the user's
imagination. Find out more about netcat at the official
website.
10. Putty
Although putty is not a hacking software by itself, it is a very useful
tool for a hacker. It is a client for SSH and telnet, which can be used
to connect to remote computers. You may use putty when you want to
connect to your Backtrack machine from your Windows PC. It can also be
used to perform SSH tunneling to bypass firewalls.